When customers come to us, they often have a specific challenge on their minds: “How do I protect my network?” “Is my cloud environment secure?” “How can I lower my storage costs?” These are critical questions, but they’re often just one piece of a much larger puzzle. At DataEndure, we understand that the universe of IT and cybersecurity is far bigger than any single issue. Every aspect of your digital… Read More
Why Network Security Must Be Your First Priority
For decades, businesses treated their networks like plumbing—an invisible utility that simply worked, delivering data from point A to point B. But today’s reality is far more complex. Your network isn’t just infrastructure; it’s the backbone of your organization’s security. If you’re still relying on legacy designs, you’re leaving yourself vulnerable in a world where threats evolve faster than ever. Today, the network and threats have changed, and your thinking… Read More
Why Digital Resilience Demands a Unified Approach
When DataEndure marked its 40th anniversary, our CEO Kurt Klein reflected on how our mission has evolved: “If you look at us 40 years ago, we were all about resilience and data protection. That’s still true today, but the demands have become more complex and multifaceted.” Today, digital resilience isn’t just an advantage—it’s a necessity. Resilience means having the ability to adapt, recover, and thrive amidst ongoing technological, operational, and… Read More
The Backup Fallacy: Why Data Protection Alone Won’t Stop Ransomware
Is data protection enough to stop ransomware in its tracks? Not quite. In this TECH Talk, you’ll discover why air-gapped backups, immutability, and access controls are key to recovery. Plus, we’ll show how IT and security teams can join forces—because simply backing up your data isn’t enough to outsmart today’s cybercriminals. Join our livestream on Thursday, 9/26. Co-hosts: Shahin Pirooz, DataEndure’s CTO & CISO Kirstin Burke, DataEndure’s CMO
Human and AI Synergy in Modern Security
While cutting-edge augmented intelligence (AI) technologies are becoming increasingly adept defending against cyber threats, the human factor remains indispensable. Listen to gain a deeper understanding of how to effectively combine human expertise and advanced technologies to fortify your cybersecurity posture. 0:00 Introduction 0:22 Augmented Intelligence Explained 1:58 Enhancing Human Capabilities 3:31 AI in Cybersecurity 5:49 Role of Human Analysts 9:01 Practical Tips and Challenges 20:00 Summary and Final Thoughts
Holidays are for Hacking: 5 Reasons Cybercriminals Target Your Downtime
While you and your team are out of the office enjoying downtime, this is when hackers get to work. Adversaries intentionally pick times when it’s difficult for your team to respond—such as evenings, holidays, and weekends. Take, for instance, car dealership SaaS platform CDK Global. They experienced a breach during the Juneteenth holiday, and then suffered another breach as they were starting to restore their systems. As of this writing,… Read More
Human and AI Synergy in Modern Security
While cutting-edge augmented intelligence (AI) technologies are becoming increasingly adept at defending against cyber threats, the human factor remains indispensable. Join us for our June TECH Talk: Human and AI Synergy in Modern Security We’ll delve into: The essential role of human expertise in the realm of augmented intelligence (AI) Examples of improved security outcomes by combining human expertise with AI The challenges of integrating human expertise with AI and… Read More
Strategies to Operationalize Cybersecurity for Enhanced Data Protection
Organizations are navigating a perfect storm in data protection, driven by a rapidly evolving threat landscape and the exponential growth of data. With global data volumes projected to reach 175 zetabytes by 2025, the need for robust cybersecurity measures to protect that data has never been more critical. Operationalizing security measures is essential to effectively safeguard any organization’s vast amount of sensitive information. 8 Strategies to Operationalize Data Protection Operationalizing… Read More
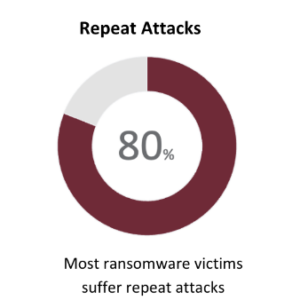
Why 80% of Ransomware Victims Suffer Repeat Attacks
In the realm of cybersecurity, the adage “lightning never strikes the same place twice” doesn’t apply. Organizations that have suffered one cyberattack are commonly targeted again, regardless of company size or industry. Ransomware by the Numbers Why Do Attackers Repeatedly Target the Same Company? The first cyberattack yields detailed insights into a company’s security architecture and response protocols. This intel becomes invaluable for orchestrating subsequent attacks that are often more… Read More
The New Frontier in Cybersecurity: A Swift Threat Response
Today’s digital age is a lot like the wild west. Cyber threats are like those old-time outlaws, always looking for a way to sneak into your operations. And just like in those classic westerns, it’s not enough to know there’s a bandit around; you’ve got to be quick on the draw to respond. That’s where we see a lot of businesses facing a real challenge. The Wild West of Cyber… Read More